Risk Crew Resources
Resources GRC resources Resource Type Article Blog GRC blog ISO 42001 - AI Management System blog
ISO 42001: Key Insights You Need to Know
Introducing ISO 42001 – the world’s first international management system standard focused specifically on AI. [...]
Blog GRC blog ISO 27001 blog Resources GRC resources Resource Type Article
ISO 27001 Requirements | Your Roadmap to Compliance
Data breaches and cyberattacks have become daily concerns for information security professionals and business leaders. [...]
Resources GRC resources Resource Type Discovery Session
DORA | DISCOVERY SESSION
Blog Resources GRC resources Resource Type Guide
DORA Compliance Checklist | GUIDE
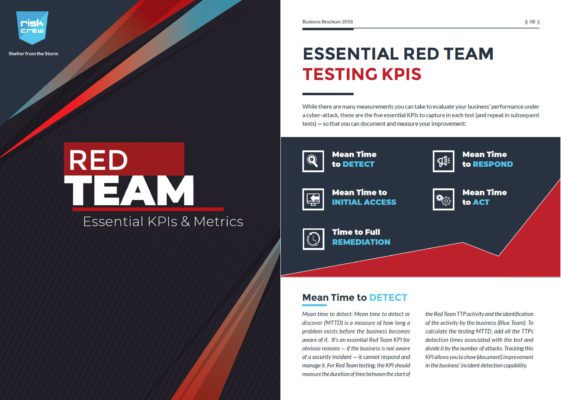
Security Testing resources Resource Type Guide Blog Resources
Essential Red Team KPIs & Metrics | GUIDE
Blog Security Testing blog Penetration Testing blog Resources Resource Type Article
How to Get Ready for a Penetration Test
It is an undeniable fact that all applications and infrastructures are essentially in need of [...]
Blog GRC blog ISO 42001 - AI Management System blog Resources GRC resources Resource Type Article AI Governance blog
Ideation to Execution: Building Your AI Governance Framework
AI governance is the foundation of responsible AI usage. It’s a framework of policies, practices [...]
Article Blog GRC blog ISO 42001 - AI Management System blog Resources GRC resources Resource Type
Stay Ahead of UK AI Regulations: Ensure Compliance Early
As artificial intelligence continues to reshape the way we all work and how enterprises operate, [...]
GRC blog DORA blog Resources GRC resources Article Blog
Essential Information | The DORA Regulation in the UK
How Does DORA Apply in the UK? Although the Digital Operational Resilience Act (DORA) is [...]
Resources GRC resources Resource Type Article Blog GRC blog DORA blog
DORA Compliance Checklist to Actionable Steps
Achieving compliance with the Digital Operational Resilience Act (DORA) may seem challenging, but with the [...]
Resource Type Article Blog GRC blog DORA blog Resources GRC resources
An Overview to DORA’s Regulatory Technical Standards (RTS)
What is DORA and How Does it Differ from Existing Risk Management Frameworks? Well, DORA [...]
Blog Risk Management blog Virtual CISO blog Resources Risk Management resources Resource Type Article
Enhancing Security and Efficiency with CISO-as-a-Service
Many organisations are turning to implementing a CISO-as-a-Service option. The service is not only efficient, [...]
Resources GRC resources Resource Type Discovery Session
Complimentary ISO 27001 | DISCOVERY SESSION
Benefits of the ISO 27001 Gap Assessment
Blog GRC blog GRC resources Resource Type Article
SAMA Cybersecurity Framework Compliance: Benefits and Requirements
Understanding SAMA’s Cyber Security Framework Due to the increasing ubiquity of cyber-attacks, the financial sector [...]
Resources GRC resources Resource Type Article Blog GRC blog DORA blog
A Complete Guide to the Digital Operational Resilience Act (DORA)
Trying to understand DORA? Think of it like this: The Digital Operational Resilience Act (DORA) [...]
Resources GRC resources Resource Type Article Blog GRC blog ISO 42001 - AI Management System blog
AI Governance – Secure the Future by Embracing Responsible AI Practices
AI in Simple Terms At its core, AI is simply software that can ‘think’, ‘learn’, [...]
Blog GRC blog ISO 27001 blog Resources GRC resources Resource Type Article
Four ISO 27001 Compliance Key Areas You Should Know
Many things that are important in getting ISO 27001 compliant but in this blog post, [...]
Blog Resources GRC resources Resource Type Guide
SOC 2 Timeline and Checklist | GUIDE
Article Blog GRC blog ISO 27001 blog Resources GRC resources Resource Type
How to Establish a Clear Desk & Clear Screen Policy for Your Organisation
You know that feeling when you walk into an office, and it looks like a [...]
GRC resources Resource Type Article Blog GRC blog NIS2 blog Resources
NIS2 Directive Timeline & Requirements to Minimise Risks
NIS 2 is Changing It’s getting Risky out there… The protection of our networks and [...]
GRC blog ISO 27001 blog Resources GRC resources Resource Type Article Blog
How to Get Ready for Your ISO 27001 Audit
In the world of information security, there are many frameworks and countless guidelines. But among [...]
Blog Risk Management blog Incident Management blog Resources Resource Type Article
How to File a Data Breach Compensation Claim
What is a Data Breach Claim? “Someone stole my personal information and I want something [...]
Blog GRC blog ISO 27001 blog Resources GRC resources Resource Type Article
ISO 27001: Steps to Write a Statement of Applicability
ISO 27001 Statement of Applicability A central component of becoming compliant with ISO 27001 is [...]
Resource Type Article Blog Risk Management blog Data Protection and Privacy blog Resources Risk Management resources
Navigating PPI Principals of GDPR for Small Businesses
“So, all we have to do to implement these 11 chapters containing 91 articles in [...]
Security Testing resources Resource Type Article Blog Security Testing blog Penetration Testing blog Resources
Importance of Black Box Testing for Your Cyber Security Defence
In a world where the digital landscape keeps changing, how can we effectively protect our [...]
GRC blog SOC 2 blog Resources GRC resources Resource Type Article Blog
Preparing for a SOC 2 Audit? Follow These 5 Key Steps
Thinking About Getting Your Cloud Platform SOC 2 Compliant? If your company handles sensitive data, [...]
GRC blog ISO 42001 - AI Management System blog Resources GRC resources Resource Type Article AI Governance blog Blog
Don’t Be Afraid of AI. Treat It Like an Insider Threat
If artificial intelligence wants to be human so badly, let’s start treating it like one. [...]
Blog Security Alerts blog Security Testing blog Red Team Testing blog Resources Security Testing resources Resource Type Article
Why a Red Team Security Assessment is Crucial for Every Business
In today’s digital age, businesses are more vulnerable than ever to cyber-attacks. As a result, [...]
Article Blog Security Testing blog Penetration Testing blog Resources Resource Type
How Much Does Penetration Testing Cost?
Penetration testing, also known as ethical hacking or white-hat hacking, is like putting on a [...]
GRC blog ISO 27001 blog Resources GRC resources Resource Type Case Study Blog
How Agrimetrics Successfully Attained ISO 27001 Certification | CASE STUDY
About the Company Agrimetrics, founded in 2014, is a leading Agri-tech Centre dedicated to revolutionising [...]
GRC resources Resource Type Article Blog GRC blog ISO 27001 blog Resources
ISO 27001 Clauses 4-10: Your Complete Guide
ISO/IEC 27001 is an international standard for creating an information security management system (ISMS). It [...]
Resource Type Article Blog Security Testing blog Red Team Testing blog Resources Security Testing resources
7 Key Benefits of Red Team Testing
In an information or cyber security context, a Red Team is a group of ethical [...]
Blog Risk Management blog Supply Chain Risk Management blog Resources Resource Type Article
Cyber Security Supply Chain Challenges in the Agrifood Industry
Guest Contributor: Benjamin Turner, Former Chief Operating Officer, Agrimetrics Shortly after Russia’s invasion of Ukraine, [...]