Information Security Policy Development
Information security policies are the foundation of an effective information security governance, risk and compliance strategy. As such, they must be based upon a well-defined strategy that clearly reflects the business’s risk appetite, tolerance and capacity for a breach. Security policies are risk-driven and must recognise that while they cannot prevent a breach, they most certainly help to identify, minimise and manage the risk of a breach.
They must be clear, concise and written in plain language so that they are easily understood by all affected parties. Because of their importance, these policies must be properly created, accepted and validated by the board and senior management before being communicated throughout the business.
Good policies are not easily produced. They must specify requirements, defines the roles and responsibilities in the business, and outline expected behaviours in various situations. They also need to satisfy internal and external compliance and audit requirements and so require a clear framework.
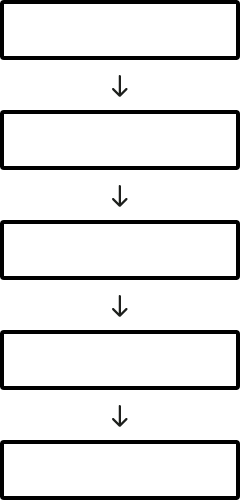
A policy framework serves to define different types of documents and their contents. They can be simple or complex depending on the business. Although, a business may have a stand-alone cybersecurity policy, it should be part of a principal information security policy framework.
Good clear policies are essential in the best of times – in uncertain times, they are critical. Risk Crew can also help you create your “work from home” policies to ensure your staff protect your information assets when working remotely.