‘Massive’ YouTube content creator hack confirmed – 23 million influencers and creators could be affected.
If you, like me have memories of just three TV channels, recording the Top 40 on your cassette player and of course the board game Battleship then the phrase social media influencer may have you scratching your head, set your teeth on edge or something in-between.
It turns out though, in marketing terms at least, that it’s important stuff. Google rewards content and it really rewards video content. Creating content and getting as many followers as possible on your YouTube channels is a full-time job in some corners. So perhaps it’s not that surprising that a very large, coordinated attack has been levelled at a hereto YouTube creators and influencers
I’ve heard some commentators refer to it as a ‘sophisticated attack – but was it really?
In some ways, it was and, in some ways…not so much. It seems that the perpetrators got hold of a gigantic list of YouTube influencers, they then undertook a targeted spear phishing campaign against this list. …And this is where it goes from sophisticated to just a bit plain old-fashioned. A spoof Google credentials log-in page was created, users were encouraged to enter their credentials into the page, credentials were harvested by the bad people and et voila! Users found their content being marked as deleted while the hackers had taken the simple steps necessary to appropriate their content and move it to the fraudulent owner along with new vanity URL.
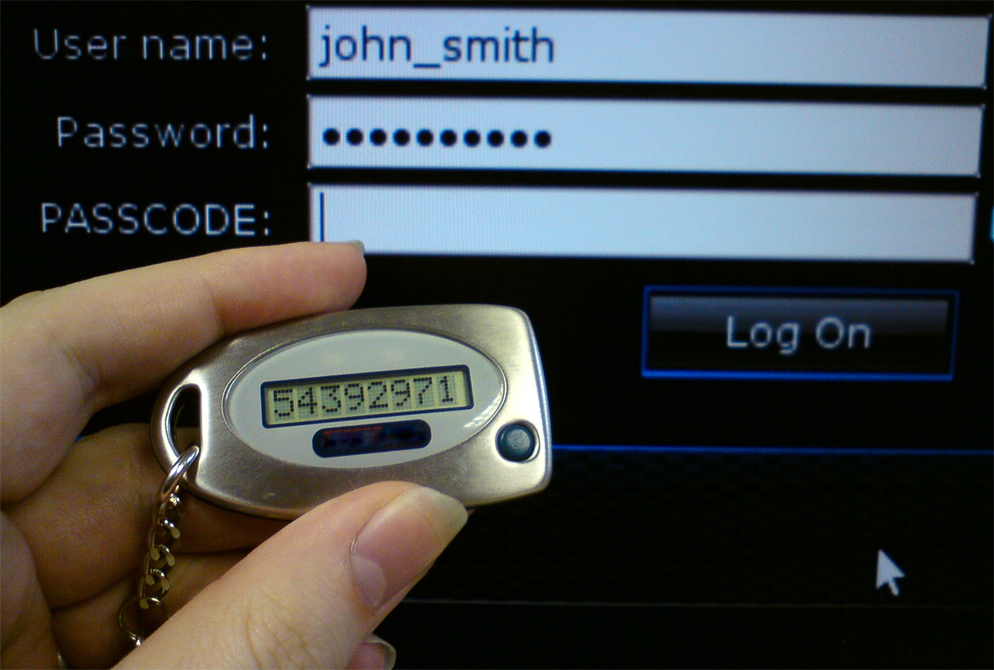
Davey Winder, in his Forbes article, suggests that seeing as some of the accounts suffering the hacking employed 2FA – that’s the two-factor authentication system designed to mitigate credential breach – the hackers could likely have employed an SMS intercepting reverse proxy toolkit.
It’s not only high-profile YouTubers who get targeted in this way by cybercriminals
Other popular online personalities also got their accounts on Twitter hacked via a very similar method. Influencer Amanda Cerny went to Twitter to express her frustrations after she regained accesses to her account. She blamed human error at US cellular provider AT&T for her account getting hacked.
Second time My phone number was hacked because of human error within company at @ATT ?! I have all possible steps of verification added after the first time again and my account was still compromised… time to switch carriers. Be careful out there everyone.
— Amanda Cerny (@AmandaCerny) August 23, 2019
The mass Twitter hacking, including CEO of Twitter, Jack Dorsey, was somewhat aided by AT&T, perhaps they and other cellular providers could do with refreshing their InfoSec Awareness programmes. If you would like to learn why information security awareness is so important, read our blog post on the topic here.
 So, if even 2FA didn’t stop the attack, what chance do we poor users have?
So, if even 2FA didn’t stop the attack, what chance do we poor users have?
Fear not – all is not lost, firstly – if the users had been information security-aware – in this case, learning how to spot a phishing email and being aware of the dangers of entering credentials on to an online form, they would never have got themselves into the position where they needed to rely on 2FA in the first place. Secondly, and this is down to user education again if they were aware that SMS based 2FA (essentially, getting a code via an SMS message to your device) is fast being seen as the weak link in 2FA or MFA (multi-factor authentication) they wouldn’t have employed this system.
Frankly speaking though, it’s not your users’ job to go out and find this information out for themselves. It’s your job and your responsibility to make sure that they are armed with this information.
And it’s our job, at Risk Crew, as specialists to help organisations in creating information security-aware cultures.
Risk Crew’s job is to Inspire your users by delivering thought-provoking content to your users face-to-face. And then Empower them by giving them access to short & snappy, multi-media rich eLearning modules and then Engage them by presenting them with a constant flow of news alerts, Infographics, videos, podcasts, newsletters, white papers and tips & tricks. Finally, it’s down to you & us to work together to Measure their progress and subsequent level of awareness by testing them via various metric & KPI collecting means.
But we can only do our job if you bring us in to help your organisation develop information best practices and create a secure culture to help prevent breaches.
Contact us to have a chat or book a demo to discover how we can help you with designing a bespoke information security awareness programme that we call eRiskology.