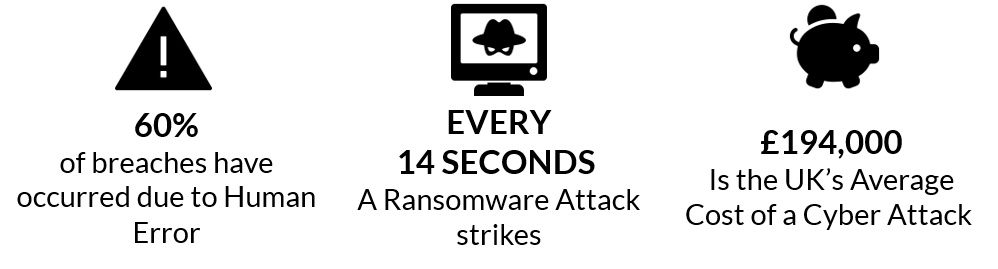
Employee error still reigns as the number one threat for data breaches even with modern day security solutions. The numbers don’t lie, with anywhere from 70 – 80% of all breaches being attributed to staff. Yet many organisations do not have a mature information & cyber security awareness programme in place.
As we mentioned in our blog piece ‘The Information Security Paradox’, those tasked with protecting the information assets of their companies are often seduced into outlaying huge financial sums by the shiny baubles of software security solutions whilst neglecting the human factor. And ironically, the more effective your IT security barriers are, the more pressure is put on the user.
The top mistakes employees make
- Responding to phishing emails by revealing credentials
- Falling for Business Email Compromise (BEC) phishing attacks
- Inadvertently allowing malware to be installed on their devices
- Not protecting data properly (I.e. leaving laptops open in public spaces / losing devices)
What you can do to prevent human error
- Regular, carefully thought-out simulated phishing campaigns that seek to educate and not point finger of blame
- Keep staff engaged by highlighting recent examples of BEC and demonstrating where and how the threat could have been mitigated
- Clear, interesting and well-articulated company policies & procedures reinforced with employee awareness training
- Run a comprehensive 3-year Information Security Awareness Programme (in other words, all the above plus much more!)
Prevent data breaches with a mature security programme
A mature security awareness programme includes learning methods that develop a cyber secure culture and will help your organisation prevent future data breaches. Test your employees to get a baseline of effectiveness, then train and educate them by:
Inspiring them with face-to-face workshops.
Empower them with cutting-edge best-practice aligned eLearning.
Engage them with regular Information & Cyber Security dispatches across varied media types.
Measure your organisations’ progress by performing socially engineered attacks, capturing metrics and KPI’s through more ongoing testing and quizzes. Thus turning your weakest link in to your first line of defense.
What drives engagement with information security
According to the Cyber Security Breaches Survey 2019 the top motivating factors for investing in various information security measures were having a breach in the past, fear of compromising customers’ financial, tax or medical records, fear of attacks becoming increasingly sophisticated, adopting new digital modes of service delivery, banking, migrating data to new servers or to the cloud, allowing more flexible remote working among employees or suppliers and GDPR.



