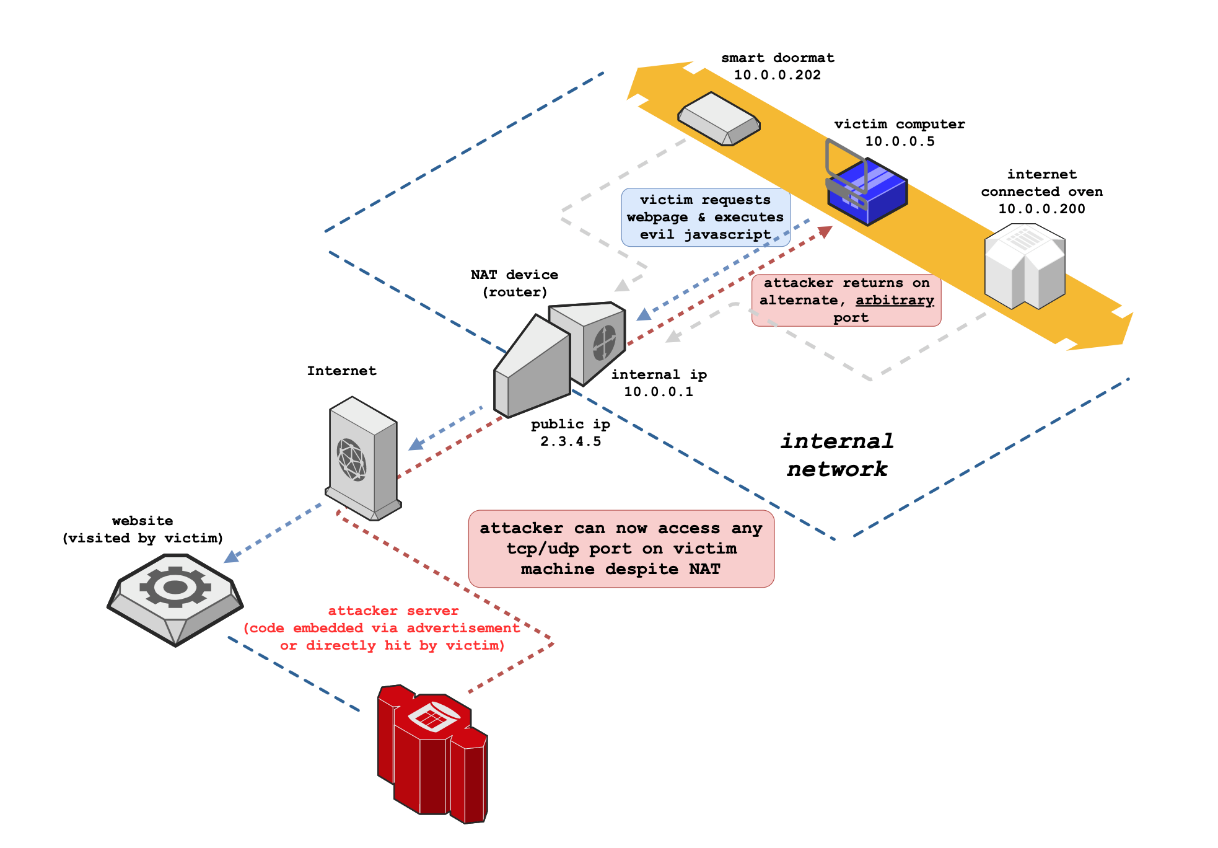
Security researcher, Samy Kamkar, has discovered a technique that allows an attacker to bypass NAT/Firewall protections, leading to remote access of any TCP/UDP port service on the target system.
Dubbed “NAT Slipstreaming”, this attack involves social engineering, the attacker sends the victim a link to a malicious site or a legitimate site with adware. When they visit the site, the attacker can open any TCP or UDP port on the victim’s system, bypassing client-side port restrictions.
The impact:
Because an attacker has successfully bypassed Firewall protections, it is now possible to gather information on and potentially exploit TCP/UDP services.
However, it is important to realise that this is an attack which demonstrates the impact of social engineering, it doesn’t matter if the Firewall is configured properly, this attack relies on deception rather than a misconfiguration or vulnerability. Finally, the researcher has released a proof of concept, which could be leveraged for malicious purposes: https://github.com/samyk/slipstream
The remediation:
This attack can be mitigated by raising awareness of social engineering attacks. Tailored social engineering training along with phishing campaigns can be effective mitigation, as it addresses the root cause of a successful phishing attack — human error.
For example, an internal phishing campaign can identify employees who are vulnerable to social engineering attacks. The purpose of this is not to name or shame, but to aid in their awareness, reducing the likelihood of falling prey in a genuine social engineering attack.
Source: The Hacker News

